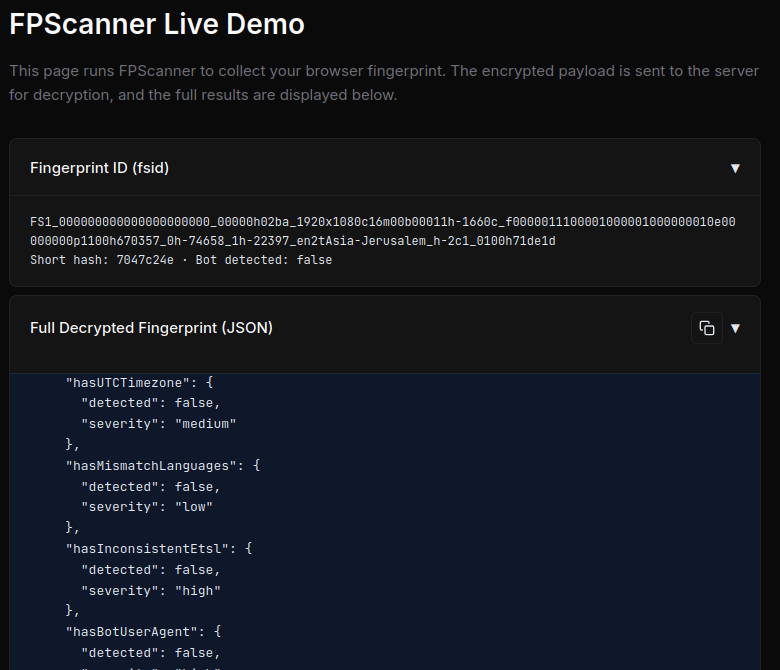
on preventing replay attacks

Replay attacks are a constant threat for websites currently protected by typical bot management solutions.
Back when we started research into these products two years ago, the obfuscation on multi-billion dollar companies' solutions was laughable - a simple array of strings, maybe with a small shuffle operation. Many companies used javascript-obfuscator. (1)
The packets sent to the server though? Very easy to replace. Often, there wasn't even a timestamp included, which means that you can for as long as you want reuse a given packet to regenerate bypass cookies.
In other words, the website was not protected at all.
Soon though, companies like HUMAN security (nothing says humanity like having to say it explicitly in your name) implemented key obfuscation per-version, which did mitigate some replay attacks. No longer could you send PX503 and the like, but you actually had to parse out each version using regex if you like waking up at strange hours and all your bypass breaking, and AST if you are sane.
^(.*?,){11}P
Beautiful.
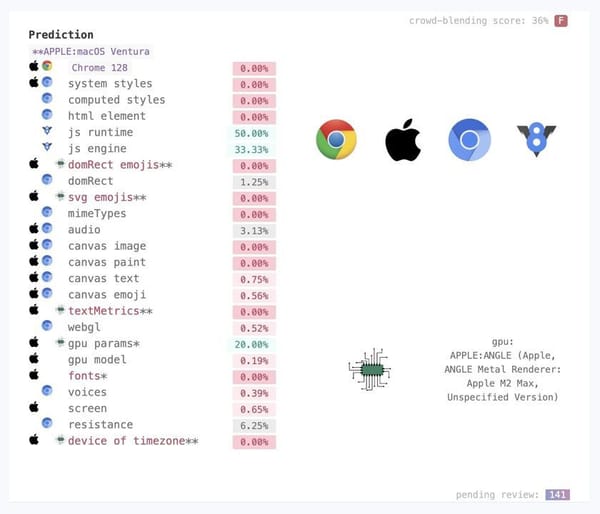
But the story doesn't stop there. I started pushing for antibots (colloquially called bot managers by the uninitiated) to use Javascript Virtual Machines here. Around this time, there were reports of some big companies whose researchers were finally able to convince their bosses to do the switch:

Which is really good for everyone, if I'm being honest. Raising the bar makes good researchers better on all sides, and pushes the script kiddies further out.
Unfortunately the actual gathered data of these companies remained the same, and alas, as such, most are still vulnerable to replay attacks, advanced stealth browsers, and advanced request bots either parsing solver style, or executing in a crafted sandbox.
But at least one battle won.
Till next time!
- (which now has vibe-coded VM protection, which is a bit sad as their obfuscation is quite good if not overused).